Bitrefill Targeted in Cyberattack Linked to North Korean Hacking Groups
By: Isha Das
Cryptocurrency e-commerce platform Bitrefill recently confirmed that it fell victim to a cyberattack on March 1. This attack, orchestrated using sophisticated methods, has been linked to the infamous North Korean hacking group known as the Lazarus Group. Bitrefill, which facilitates the exchange of digital currencies like Bitcoin and Dogecoin for gift cards, issued a statement that attributes the breach to tactics associated with Lazarus Group, a well-documented cybercriminal organization.
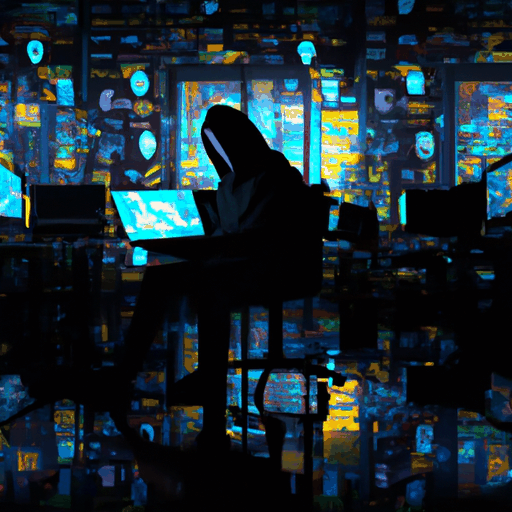
The incident remains significant as it highlights the continuous cybersecurity threats faced by companies in the cryptocurrency sector. The hackers exploited Bitrefill by infiltrating an employee's laptop, using malware, on-chain tracing, and repeating known IP and email infrastructures. This breach led to a drain of funds from Bitrefill's hot wallets and unauthorized access to approximately 18,500 purchase records. Despite the severity of the attack, Bitrefill did not disclose the exact amount of money stolen but assured that they would cover the losses through operational capital. Ensuring the safety and privacy of their customers, Bitrefill emphasized that only limited customer information was exposed.
A notable aspect of this breach is its potential connection to BlueNoroff Group, another North Korean entity with suspected ties to Lazarus Group. Given the similarities in their cyber tactics, it's possible that both groups collaborated or that BlueNoroff was independently responsible. The incident underscores the vulnerability of cryptocurrency platforms to nation-state actors and highlights the need for enhanced security measures across the industry.
Bitrefill’s disclosure serves as a reminder to other companies in the cryptocurrency space to remain vigilant and prioritize cybersecurity. The event has sparked concerns and discussions regarding the persistent threat posed by state-sponsored hacking groups, particularly those linked to North Korea. As the investigation continues, it emphasizes the critical importance of robust cybersecurity protocols, employee training, and systemic oversight to protect against future breaches.